Framework Architecture
Layered Model
A web application uses a mechanism specified in this document to gain access to (or bind to) a JavaScript API by stating one or more features exposed by the JavaScript API. This access is given on a basis of the trust domain that has been assigned to the web application. The implementation of the API, in turn, makes use of one or more device capabilities, defined in terms of facilities that might be provided by APIs at the device, platform or OS level, but without reference to any particular API. Where a JavaScript API is defined within the this model, each function definition specifies which feature it implements, and which device capabilities it uses.
The mechanisms provided in this specification to bind to APIs, and to control access (both to the features and the device capabilities exposed by them) are generic, and are not themselves dependent on any particular set of JavaScript APIs. This model envisages that these controls apply, irrespective of whether the APIs in use are defined by DAP or any independent entity.
Trust Domain Control Layer
The trust domain control layer controls the assignment of the appropiate trust domain to the web application via the relevant trust policy. In general, trust policies will select one trust domain or another depending on the subject attributes and environment attributes that identify the web application.
JavaScript API Access Control Layer
The JavaScript API access control layer controls access to JavaScript APIs exposed by the web runtime. Each feature is identified uniquely by IRI, and this security layer mediates access to features on the basis of that ID.
Device Capability Access Control Layer
The device capability access control layer controls access to the underlying capabilities of the device when used from JavaScript APIs. These device capabilities themselves are identified so that it is possible to write security policies that control access to specific capabilities independently of the JavaScript APIs used to access them.
For both JavaScript API and device capability access control layers, access permissions are guaranteed or restricted on a basis of via access control policies. In general, access control policies will select the effect of a particular access request depending on the resources attributes captured when the request happened.
Considerations
This explicit separation of features and their dependent device capabilities addresses a number of significant requirements, as follows.
Extensibility is an intrinsic part of the security model. It is expected that APIs will be defined and implemented independently, and the nature of those APIs will not necessarily be known to the author of a security policy. Therefore, if a security policy author wishes to deny access to a specific device capability, then there must be a way of doing this that is independent of the JavaScript API being used.
The web runtime must only grant access to features that are advertised as being dependencies of the web application. The access control system must ensure that only requested features are accessible to the web application. This requires that the access control system is able to control access based on the ID of a Feature.
There will not be a direct 1-1 correspondence between JavaScript APIs and device capabilities. Although there will be simple JavaScript APIs that provide access only to a single device capability, it must be expected that there are also more complex APIs that expose multiple device capabilities; examples might include a camera API that provides the ability to geotag a photo with the current location, or a messaging API that provides the ability to access documents stored locally and attach them to outgoing messages. Therefore, enabling or disabling access to a specific device capability will not directly correspond to enabling or disabling access to a single JavaScript API.
Implementations of JavaScript APIs need not be as highly trusted as the web runtime. Authors of access policies may require the ability to control access to specific JavaScript APIs, or families of APIs, based on the identity of the API (and not just the device capabilities it exposes), according to the trustworthiness of the author of the API.
It must be possible to represent both trust and access policies portably. This implies that all identifiers used in a security policy (both for features and for device capabilities) must be portably defined, and not (for example) based on any platform-specific API names. This requires that the identifiers for device capabilities are defined in a platform-independent way.
Logical Model
On the one hand, the trust domain control system explained in this document, from a logical perspective, represents the system by which a web application that attempts to access device capabilities using JavaScript APIs, is assigned a trust or security domain. This trust domain will then be used in subsequent access requests, simplifying the whole process. On the other hand, the access control system, implementing a specific access control policy, has the sole effect of making and enforcing an access control decision in relation to each attempted access. (In order to make that decision the access control system may request interactive confirmation from the user, but this is invisible to the requesting web application.)
Both the trust and access control systems consist of a number of logically distinct elements. This logical breakdown and associated terminology is adopted from XACML [[XACML20]] and illustrated below.
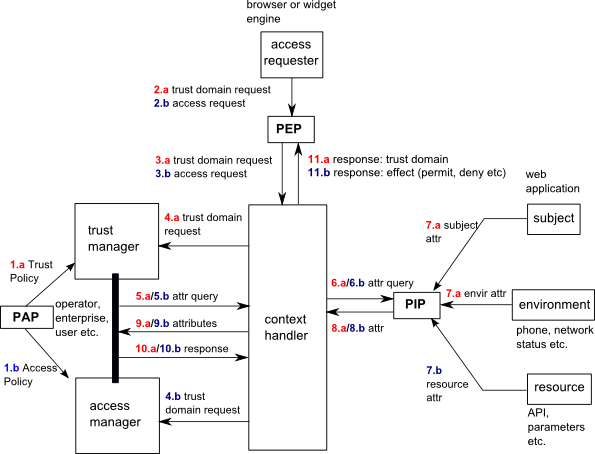
The specified functional components are as follows:
Policy Decision Point (PDP): for trust domain requests, the module that evaluates which trust domain should be assigned to a web application; for access requests, the module that evaluates whether or not a device API can be accessed by a web application, based on the current policy.
Policy Enforcement Point (PEP): for trust domain requests, the module that assigns a trust domain to a particular web application; for access requests, the module that allows or prevents access to device APIs.
Policy Information Point (PIP): the module that gathers information to be used by the PDP to evaluate a trust domain or an access control request. For trust domain requests, it collects the subject attributes (i.e. how the web application was identified and its associated security attributes), whereas for access requests, resource attributes (i.e. which device API is being requested and using which parameters) and environment attributes (i.e. status of the device) are collected.
Policy Administration Point (PAP): the authority that defines the policy. It could be a network operator, a terminal manufacturer, a web runtime developer, an enterprise or a user at runtime. Policies can be provided by the PAP in different ways, for instance using a preloaded file or data structure, or a remote management mechanism (e.g. OMA DM [[OMA-DM]]).
OMA DM reference missing?
Should we include this?: In the present phase, DAP does not define any specific external interface requirements for the PAP, although this may be in scope for later phases. The security policy itself is not defined by DAP, although a default policy may be recommended by DAP at a future stage.
The functionality required in each of these components is specified in terms of the following entities:
- subject
the web application that requires access to JavaScript APIs. Examples of subjects are websites and widgets.
An entity that may attempt security-relevant actions and corresponds to a single "identity". (In practice, some web applications might have multiple identities – for example is a widget resource is signed by multiple signers – but for the purposes of this model, each access control query is considered to involve a single subject and hence a single identity.)
The website identity type applies to all operations occurring in the execution of a remotely-hosted document, whether this is the top-level document of the website or is associated with some child browsing context (such as an iframe).
- subject attribute
Every subject is associated with a set of attributes. Subject attributes allow the identification of the web application that is attempting access to device capabilities using device APIs. The identified web application is then assigned a trust domain according to the appropriate trust policy. Subject attributes include specific attributes that represent the identity of the web application attempting access to a resource. Valid identity attributes include the widget identifier URI for widgets and the URL for websites; other identifiers may be supported. Subject attributes also include the credentials used to verify the authenticity and integrity of the subject, e.g. a TLS or code signing digital certificate. Other credentials may be supported.
All subject attributes are determined for the applicable application execution phases: widget-install, widget-instantiate.
- resource
-
the resources that subjects may request access to. The device features or services (e.g. the location module or PIM database) are the actual resources that are being protected, but from the point of view of the security framework these resources are associated with the API Features and device capabilities used to access them.
The widget identity type applies to all operations associated with a widget resource, or occurring in the execution of a document belonging to a widget resource.
Operations occurring in the execution of a remotely hosted document that has been loaded by a widget (for example in an iframe) use a website identity.
- resource attribute
Every resource is associated with a set of attributes. Resource attributes include an identifier. Other attributes may be associated with a resource, and these can include specific parameters that are specified as part of the request when attempting access. Resource attributes serve as input of access control policies.
The device features or services (e.g. the location module or PIM database) are the actual resources that are being protected, but from the point of view of the security framework these resources are associated with the API features and device capabilities used to access them.
- environment attribute
The collection of device status and context attributes that may be relevant to the circumstances of a resource access attempt, but are not directly associated with either the subject or resource. For example, environment attributes can include terminal charging, network connection status, whether roaming. Environment attributes serve as input of access control policies.
Attributes of the environment capture contextual information relating to the device or other circumstances of the access attempt.
Application Execution Phases
The execution phase of a web application reflects the state of that application at the time an associated trust domain or access control query is made. The defined execution phases are listed below.
| Execution Phase | Description |
|---|---|
| widget-install | Applies to trust domain or access control queries made by a widget user agent during the processing of a widget resource as part of an installation or update operation. |
| widget-instantiate | Applies to trust domain or access control queries made by a widget user agent during the instantiation of a widget. |
| website-bind | Applies to access control queries made in response to a call to requestFeature() in the course of execution of a website |
| invoke | Applies to access control queries made in response to invocation of a JavaScript API in the course of execution of a web application |
Need to define "requestFeature()" ?
In BONDI, the requestFeature() API is itself a Feature. Websites have access to this API automatically and this is the sole means of expression of Feature dependencies by Websites.